Abstract
The EnRUPT hash functions were proposed by O’Neil, Nohl and Henzen [5] as candidates for the SHA-3 competition, organised by NIST [4]. The proposal contains seven concrete hash functions, each having a different digest length.
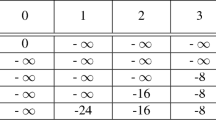
We present a practical collision attack on each of these seven EnRUPT variants. The time complexity of our attack varies from 236 to 240 round computations, depending on the EnRUPT variant, and the memory requirements are negligible. We demonstrate that our attack is practical by giving an actual collision example for EnRUPT-256.
Chapter PDF
Similar content being viewed by others
References
Canteaut, A., Chabaud, F.: A New Algorithm for Finding Minimum-Weight Words in a Linear Code: Application to McEliece’s Cryptosystem and to Narrow-Sense BCH Codes of Length 511. IEEE Transactions on Information Theory 44(1), 367–378 (1998)
Chabaud, F., Joux, A.: Differential Collisions in SHA-0. In: Krawczyk, H. (ed.) CRYPTO 1998. LNCS, vol. 1462, pp. 56–71. Springer, Heidelberg (1998)
Lipmaa, H., Moriai, S.: Efficient Algorithms for Computing Differential Properties of Addition. In: Matsui, M. (ed.) FSE 2001. LNCS, vol. 2355, pp. 336–350. Springer, Heidelberg (2002)
National Institute of Standards and Technology, Announcing Request for Candidate Algorithm Nominations for a New Cryptographic Hash Algorithm (SHA-3) Family, Federal Register 72(212), pp. 62212–62220 (2007)
O’Neil, S., Nohl, K., Henzen, L.: EnRUPT Hash Function Specification. Submission to the NIST SHA-3 competition (2008), http://www.enrupt.com/SHA3/
O’Neil, S.: Personal communication (January 20, 2009)
O’Neil, S.: EnRUPT. In: The First SHA-3 Candidate Conference, Leuven, Belgium, February 25–29 (2009), http://csrc.nist.gov/groups/ST/hash/sha-3/Round1/Feb2009/documents/EnRUPT_2009.pdf
Pramstaller, N., Rechberger, C., Rijmen, V.: Exploiting Coding Theory for Collision Attacks on SHA-1. In: Smart, N.P. (ed.) Cryptography and Coding 2005. LNCS, vol. 3796, pp. 78–95. Springer, Heidelberg (2005)
Rijmen, V., Oswald, E.: Update on SHA-1. In: Menezes, A. (ed.) CT-RSA 2005. LNCS, vol. 3376, pp. 58–71. Springer, Heidelberg (2005)
Viterbi, A.J.: Error bounds for convolutional codes and an asymptotically optimum decoding algorithm. IEEE Transactions on Information Theory 13(3), 260–269 (1967)
Wang, X., Yu, H.: How to Break MD5 and Other Hash Functions. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 19–35. Springer, Heidelberg (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Indesteege, S., Preneel, B. (2009). Practical Collisions for EnRUPT. In: Dunkelman, O. (eds) Fast Software Encryption. FSE 2009. Lecture Notes in Computer Science, vol 5665. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-03317-9_15
Download citation
DOI: https://doi.org/10.1007/978-3-642-03317-9_15
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-03316-2
Online ISBN: 978-3-642-03317-9
eBook Packages: Computer ScienceComputer Science (R0)