Abstract
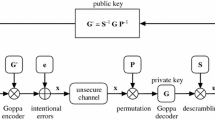
In this paper we show how to strengthen public-key cryptosystems against known attacks, together with the reduction of the public-key. We use properties of subcodes to mask the structure of the codes used by the conceiver of the system. We propose new parameters for the cryptosystems and even a modified Niederreiter cryptosystem in the case of Gabidulin codes, with a public-key size of less than 4000 bits.
Similar content being viewed by others
References
A. Canteaut F. Chabaud (1998) ArticleTitleA new algorithm for finding minimum-weight words in a linear code: Application to McEliece’s cryptosystem and to narrow-sense BCH codes of length 511 IEEE Trans. Inform. Theory 44 IssueID1 367–378
A. Canteaut and N. Sendrier, Cryptanalysis of the original McEliece cryptosystem, In (K. Ohta and D. Pei eds.), Advances in Cryptology–-ASIACRYPT’98, number 1514 in LNCS (1998) pp. 187–199.
F. Chabaud and J. Stern, The cryptographic security of the syndrome decoding problem for rank distance codes, In (K. Kim and T. Matsumoto eds.), Advances in Cryptology–-ASIACRYPT ‘96, volume 1163 of LNCS. Verlag (1996).
A. Dür (1987) ArticleTitleThe automorphism group of Reed–Solomon codes J. Comb. Theory, series A 44 69–82
A. Ourivski, E. Gabidulin and V. Pavlouchkov, On the modified Niederreiter cryptosystem, in the Proceedings of the Information Theory and Networking Workshop, ITW(1999) p.50.
E. M. Gabidulin, Theory of codes with maximal rank distance, Problems Inform. Transm., vol. 21 (1985).
E. M. Gabidulin and A. V. Ourivski, Improved GPT public-key cryptosystems, In (P. Farrell, M. Darnell and B. Honary eds.), Coding Communications and Broadcasting (2000) pp. 73–102.
E. M. Gabidulin A. V. Paramonov O. V. Tretjakov (1991) ArticleTitleIdeals over a non-commutative ring and their application in cryptology LNCS 573 482–489
J. K. Gibson (1995) ArticleTitleSeverely denting the Gabidulin version of the McEliece public-key cryptosystem Designs, Codes and Cryptography 6 37–45
J. K. Gibson, The security of the Gabidulin public-key cryptosystem, In (U. Maurer ed.), EUROCRYPT’96 (1996) pp. 212–223.
P. J. Lee and E. F. Brickell, An observation on the security of McEliece’s public-key cryptosystem, In (C. G. Günter ed.), Advances in Cryptology–-EUROCRYPT’88, volume 330 of LNCS, Verlag (1988) pp. 275–280.
P. Loidreau N. Sendrier (2001) ArticleTitleWeak keys in McEliece public-key cryptosystem IEEE Trans. Inform. Theory 47 IssueID3 1207–211
F. J. MacWilliams and N. J. A. Sloane, The Theory of Error–Correcting Codes. North Holland (1977).
R. J. McEliece, A public-key cryptosystem based on algebraic coding theory, Technical report, Jet Propulsion Lab. DSN Progress Report (1978).
H. Niederreiter (1986) ArticleTitleKnapsack-type cryptosystems and algebraic coding theory Problems of Control Inform. Theory 15 IssueID2 159–166
R. M. Roth G. Seroussi (1985) ArticleTitleOn generator matrices of MDS codes IEEE Trans. Inform. Theory 31 IssueID6 826–830
V. M. Sidel’nikov S. O. Shestakov (1992) ArticleTitleOn cryptosystems based on generalized Reed-Solomon codes Discrete Mathematics 4 IssueID3 57–63
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by: P. Wild
AMS Classification: 11T71
Rights and permissions
About this article
Cite this article
Berger, T.P., Loidreau, P. How to Mask the Structure of Codes for a Cryptographic Use. Des Codes Crypt 35, 63–79 (2005). https://doi.org/10.1007/s10623-003-6151-2
Received:
Revised:
Accepted:
Issue Date:
DOI: https://doi.org/10.1007/s10623-003-6151-2