Abstract
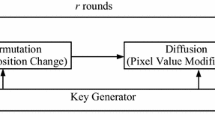
This paper presents a solution to satisfy the increasing requirement of real-time secure image transmission over public networks. The main advantage of the proposed cryptosystem is high efficiency. The confusion and diffusion operations are both performed based on a lookup table. Therefore, the time-consuming floating point arithmetic in chaotic map iteration and quantization procedures of traditional chaos-based image cipher can be avoided. Besides, this cryptosystem possesses satisfactory resistance to noise perturbation and loss of cipher data, which are inevitable and unpredictable in real-world channels. The channel disturbance and the deliberate damage from the opponents are both tolerated. The recovered image from the damaged cipher data has satisfactory visual perception. Simulations prove the advantages of the proposed scheme, which render it a good candidate for real-time secure image applications.










Similar content being viewed by others
References
Li, S., Chen, G., Zheng, X.: Chaos-based encryption for digital images and videos. In: Furht, B., Kirovski, D. (eds.) Multimedia Security Handbook. CRC Press, Florida (2004)
Alvarez, G., Li, S.J.: Some basic cryptographic requirements for chaos-based cryptosystem. Int. J. Bifurc. Chaos 16(8), 2129–2151 (2006)
Zhang, Y., Xiao, D.: Self-adaptive permutation and combined global diffusion for chaotic color image encryption. AEU Int. J. Electron. Commun. 68(14), 361–368 (2014)
Fridrich, J.: Symmetric ciphers based on two-dimensional chaotic maps. Int. J. Bifurc. Chaos 8(6), 1259–1284 (1998)
Chen, J.X., Zhu, Z.L., Fu, C., Yu, H., Zhang, L.B.: An efficient image encryption scheme using gray code based permutation approach. Opt. Laser Eng. 67, 191–204 (2015)
Wong, K.W., Kwok, B.S.H., Law, W.S.: A fast image encryption scheme based on chaotic standard map. Phys. Lett. A 372(15), 2645–2652 (2008)
Ye, G., Wong, K.W.: An efficient chaotic image encryption algorithm based on a generalized Arnold map. Nonlinear Dyn. 69(4), 2079–2087 (2012)
Mirzaei, M.Yaghoobi, Irani, H.: A new image encryption method: parallel sub-image encryption with hyper chaos. Nonlinear Dyn. 67(1), 557–566 (2012)
Zhu, Z.L., Zhang, W., Wong, K.W., Yu, H.: A chaos-based symmetric image encryption scheme using a bit-level permutation. Inf. Sci. 181(6), 1171–1186 (2011)
Zhang, W., Wong, K.W., Yu, H., Zhu, Z.L.: A symmetric color image encryption algorithm using the intrinsic features of bit distributions. Commun. Nonlinear Sci. Numer. Simul. 18(3), 584–600 (2013)
Wang, X.Y., Luan, D.P.: A novel image encryption algorithm using chaos and reversible cellular automata. Commun. Nonlinear Sci. Numer. Simul. 18(11), 3075–3085 (2013)
Fu, C., Meng, W.H., Zhan, Y.F., Zhu, Z.L., Lau, F.C.M., Tse, C.H., Ma, H.F.: An efficient and secure medical image protection scheme based on chaotic maps. Comput. Biol. Med. 43(8), 1000–1010 (2013)
Zhang, X., Wang, X.: Chaos-based partial encryption of SPIHT coded color images. Signal Process. 93(9), 2422–2431 (2013)
Zhang, W., Wong, K.W., Yu, H., Zhu, Z.L.: An image encryption scheme using reverse 2-dimensional chaotic map and dependent diffusion. Commun. Nonlinear Sci. Numer. Simul. 18(8), 2066–2080 (2013)
Tong, X.J.: The novel bilateral—diffusion image encryption algorithm with dynamical compound chaos. J. Syst. Softw. 85(4), 850–858 (2012)
Zhang, X., Zhao, Z.: Chaos-based image encryption with total shuffling and bidirectional diffusion. Nonlinear Dyn. 75(1–2), 319–330 (2014)
Tong, X.J., Wang, Z., Zhang, M., Liu, Y.: A new algorithm of the combination of image compression and encryption technology based on cross chaotic map. Nonlinear Dyn. 72(1–2), 229–241 (2013)
Zhang, Y., Xiao, D., Liu, H., Nan, H.: GLS coding based security solution to JPEG with the structure of aggregated compression and encryption. Commun. Nonlinear Sci. Numer. Simul. 19(5), 1366–1374 (2014)
Zhou, N., Zhang, A., Zheng, F., Gong, L.: Novel image compression-encryption hybrid algorithm based on key-controlled measurement matrix in compressive sensing. Opt. Laser Technol. 62, 152–160 (2014)
Yuen, C.H., Wong, K.W.: A chaos-based joint image compression and encryption scheme using DCT and SHA-1. Appl. Soft Comput. 11(8), 5092–5098 (2011)
Xiang, T., Qu, J., Xiao, D.: Joint SPIHT compression and selective encryption. Appl. Soft Comput. 21, 159–170 (2014)
Ye, G., Wong, K.W.: An image encryption scheme based on time-delay and hyperchaotic system. Nonlinear Dyn. 71(1–2), 259–267 (2013)
Wang, X.Y., Bao, X.M.: A novel block cryptosystem based on the coupled chaotic map lattice. Nonlinear Dyn. 72(4), 707–715 (2013)
Tong, X.J.: Design of an image encryption scheme based on a multiple chaotic map. Commun. Nonlinear Sci. Numer. Simul. 18(7), 1725–1733 (2013)
Tong, X., Cui, M.: Image encryption scheme based on 3D baker with dynamical compound chaotic sequence cipher generator. Signal Process. 89(4), 480–491 (2009)
Wang, Y., Wong, K.W., Liao, X.F., Xiang, T., Chen, G.R.: A chaos-based image encryption algorithm with variable control parameters. Chaos Solitons Fractals 41(4), 1773–1783 (2009)
Chen, J.X., Zhu, Z.L., Fu, C., Yu, H.: An improved permutation-diffusion type image cipher with a chaotic orbit perturbing mechanism. Opt. Express 21(23), 27873–27890 (2013)
Fu, C., Chen, J.J., Zou, H., Meng, W.H., Zhan, Y.F., Yu, Y.W.: A chaos-based digital image encryption scheme with an improved diffusion strategy. Opt. Express 20(3), 2363–2378 (2012)
Huang, X., Ye, G.: An efficient self-adaptive model for chaotic image encryption algorithm. Commun. Nonlinear Sci. Numer. Simul. 19(12), 4094–4104 (2014)
Zhang, L., Hu, X., Liu, Y., Wong, K.W., Gan, J.: A chaotic image encryption scheme owning temp-value feedback. Commun. Nonlinear Sci. Numer. Simul. 19(10), 3653–3659 (2014)
Wong, K.W., Kwok, B.S.H., Yuen, C.H.: An efficient diffusion approach for chaos-based image encryption. Chaos Solitons Fractals 41(5), 2652–2663 (2009)
Wu, Y., Zhou, Y., Noonan, J.P., Agaian, S.: Design of image cipher using latin squares. Inform. Sci. 264(20), 317–339 (2014)
Zhang, Y., Xiao, D.: An image encryption scheme based on rotation matrix bit-level permutation and block diffusion. Commun. Nonlinear Sci. Numer. Simul. 18(1), 74–82 (2014)
Shannon, C.E.: Communication theory of secrecy systems. Bell. Syst. Tech. J. 28(4), 656–715 (1949)
Chen, J.X., Zhu, Z.L., Fu, C., Yu, H., Zhang, L.B.: A fast chaos-based image encryption scheme with a dynamic state variables selection mechanism. Commun. Nonlinear Sci. Numer. Simul. 20(3), 846–860 (2014)
Wikipedia, http://en.wikipedia.org/wiki/Latin_square
Fu, C., Lin, B.B., Miao, Y.S., Liu, X., Chen, J.J.: A novel chaos-based bit-level permutation scheme for digital image encryption. Opt. Commun. 284(23), 5415–5423 (2011)
Wang, Y., Wong, K.W., Liao, X.F., Chen, G.R.: A new chaos-based fast image encryption algorithm. Appl. Soft Comput. 11(1), 514–522 (2011)
Li, C., Lo, K.T.: Optimal quantitative cryptanalysis of permutation-only multimedia ciphers against plaintext attacks. Signal Process. 91(4), 949–954 (2011)
Li, S., Li, C., Chen, G., Bourbakis, N.G., Lo, K.T.: A general quantitative cryptanalysis of permutation-only multimedia ciphers against plaintext attacks. Signal Process Image Commun. 23(3), 212–223 (2008)
Farajallah, M., Fawaz, Z., El Assad, S., Deforges, O.: Efficient image encryption and authentication scheme based on chaotic sequences. In: The Seventh International Conference on Emerging Security Information, Systems and Technologies, pp. 150–155 (2013)
IEEE Computer Society: IEEE standard for binary floating-point arithmetic, ANSI/IEEE std. 754–1985 (1985)
Wu, Y., Zhou, Y., Saveriades, G., Agaian, S., Noonan, J.P., Natarajan, P.: Local Shannon entropy measure with statistical tests for image randomness. Inform. Sci. 222(10), 323–342 (2013)
Acknowledgments
This work was supported by the National Natural Science Foundation of China (Nos. 61271350, 61374178, 61202085).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Chen, Jx., Zhu, Zl., Fu, C. et al. An efficient image encryption scheme using lookup table-based confusion and diffusion. Nonlinear Dyn 81, 1151–1166 (2015). https://doi.org/10.1007/s11071-015-2057-6
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11071-015-2057-6