Abstract
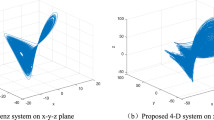
In this paper, an asymmetric hybrid cryptosystem with coherent superposition, equal modulus and random decomposition in hybrid transform domain is proposed. To further strengthen the security of the cryptosystem, a hyperchaotic system is used as a pixel-swapping procedure. The hybrid transform is generated by utilizing fractional Fourier transform of various orders and Walsh transform. The hyperchaotic framework’s parameters and starting conditions alongside the fractional orders of the fractional Fourier transform extend the key-space and consequently give extra strength to the proposed cryptosystem. The designed cryptosystem has an extended key-space to avoid any brute-force attack and is non-linear in nature. The scheme is validated on gray-scale images. Computer based simulations have been performed to verify the validity and the performance of the proposed cryptosystem against different types of attacks. Results demonstrate that the proposed cryptosystem not only offers higher protection against noise attacks but is also invulnerable to special attack.


















Similar content being viewed by others
References
Abuturab, M.R.: Group multiple-image encoding and watermarking using coupled logistic maps and gyrator wavelet transform. JOSA A 32, 1811–1820 (2015). https://doi.org/10.1364/JOSAA.32.001811
Barfungpa, S.P., Abuturab, M.R.: Asymmetric cryptosystem using coherent superposition and equal modulus decomposition of fractional Fourier spectrum. Opt. Quantum Electron 48(11), 520 (2016). https://doi.org/10.1007/s11082-016-0786-5
Biryukov, A.: Chosen Ciphertext Attack. Encyclopedia of Cryptography and Security, pp. 205–205. Springer, Boston (2011). https://doi.org/10.1007/978-1-4419-5906-5_556
Biryukov, A.: Known Plaintext Attack. Encyclopedia of Cryptography and Security, pp. 704–705, Springer, Boston (2011). https://doi.org/10.1007/978-1-4419-5906-5_588
Butcher, J.: The Numerical Analysis of Ordinary Differential Equations: Runge-Kutta and General Linear Methods. Wiley, Hoboken (1987)
Cai, J., Shen, X.: Modified optical asymmetric image cryptosystem based on coherent superposition and equal modulus decomposition. Opt. Laser Technol. 95, 105–112 (2017). https://doi.org/10.1016/j.optlastec.2017.04.018
Cai, J., Shen, X., Lei, M., Lin, C., Dou, S.: Asymmetric optical cryptosystem based on coherent superposition and equal modulus decomposition. Opt. Lett. 40, 475–478 (2015). https://doi.org/10.1364/OL.40.000475
Candan, C., Kutay, M.A., Ozaktas, H.M.: The discrete fractional Fourier transform. IEEE Trans. Signal Process. 48, 1329–1337 (2000). https://doi.org/10.1109/78.839980
Chai, X., Chen, Y., Broyde, L.: A novel chaos-based image encryption algorithm using DNA sequence operations. Opt. Lasers Eng. 88, 197–213 (2017). https://doi.org/10.1016/j.optlaseng.2016.08.009
Chen, L., Zhao, D.: Optical image encryption with Hartley transforms. Opt. Lett. 31, 3438–3440 (2006). https://doi.org/10.1364/OL.31.003438
Chen, A., Lu, J., Lü, J., Yu, S.: Generating hyperchaotic Lü attractor via state feedback control. Phys Stat Mech Appl 364, 103–110 (2006). https://doi.org/10.1016/j.physa.2005.09.039
Chen, W., Chen, X., Sheppard, C.J.R.: Optical image encryption based on diffractive imaging. Opt. Lett. 35, 3817–3819 (2010). https://doi.org/10.1364/OL.35.003817
Chen, J.-X., Zhu, Z.-L., Fu, C., Zhang, L.-B., Zhang, Y.: Cryptanalysis and improvement of an optical image encryption scheme using a chaotic Baker map and double random phase encoding. J. Opt. 16(12), 125403 (2014). https://doi.org/10.1088/2040-8978/16/12/125403
Chen, H., Tanougast, C., Liu, Z., Sieler, L.: Asymmetric optical cryptosystem for color image based on equal modulus decomposition in gyrator transform domains. Opt. Lasers Eng. 93, 1–8 (2017). https://doi.org/10.1016/j.optlaseng.2017.01.005
Chen, H., Liu, Z., Zhu, L., Tanougast, C., Blondel, W.: Asymmetric color cryptosystem using chaotic Ushiki map and equal modulus decomposition in fractional Fourier transform domains. Opt. Lasers Eng. 112, 7–15 (2019). https://doi.org/10.1016/j.optlaseng.2018.08.020
Deng, X.: Asymmetric optical cryptosystem based on coherent superposition and equal modulus decomposition: comment. Opt. Lett. 40(16), 3913 (2015). https://doi.org/10.1364/OL.40.003913
Elshamy, A.M., Rashed, A.N.Z., Mohamed, A.E.N.A., Faragalla, O.S., Mu, Y., Alshebeili, S.A., et al.: Optical image encryption based on chaotic baker map and double random phase encoding. J Light Technol 31, 2533–2539 (2013). https://doi.org/10.1109/JLT.2013.2267891
Fatima, A., Mehra, I., Nishchal, N.K.: Optical image encryption using equal modulus decomposition and multiple diffractive imaging. J. Opt. 18(8), 085701 (2016). https://doi.org/10.1088/2040-8978/18/8/085701
Frauel, Y., Castro, A., Naughton, T.J., Javidi, B.: Resistance of the double random phase encryption against various attacks. Opt. Express 15, 10253–10265 (2007). https://doi.org/10.1364/OE.15.010253
Fu, C., Zhang, G., Zhu, M., Chen, Z., Lei, W.: A new chaos-based color image encryption scheme with an efficient substitution keystream generation strategy. Secur Commun Netw (2018). https://doi.org/10.1155/2018/2708532
Gopinathan, U., Monaghan, D.S., Naughton, T.J., Sheridan, J.T.: A known-plaintext heuristic attack on the Fourier plane encryption algorithm. Opt. Express 14, 3181–3186 (2006). https://doi.org/10.1364/OE.14.003181
Hennelly, B., Sheridan, J.T.: Optical image encryption by random shifting in fractional Fourier domains. Opt. Lett. 28, 269–271 (2003). https://doi.org/10.1364/OL.28.000269
Huang, J.-J., Hwang, H.-E., Chen, C.-Y., Chen, C.-M.: Lensless multiple-image optical encryption based on improved phase retrieval algorithm. Appl. Opt. 51, 2388–2394 (2012). https://doi.org/10.1364/AO.51.002388
Javidi, B., Nomura, T.: Securing information by use of digital holography. Opt. Lett. 25, 28–30 (2000). https://doi.org/10.1364/OL.25.000028
Kekre, H.B., Thepade, S.D.: Image retrieval using non-involutional orthogonal Kekre transform. Int. J. Multidiscip. Res. Adv. Eng. 1, 189–203 (2009)
Kekre, H.B., Sarode, T.K., Vig, R.: A new multi-resolution hybrid wavelet for analysis and image compression. Int. J. Electron. 102, 2108–2126 (2015). https://doi.org/10.1080/00207217.2015.1020882
Liu, Z., Chen, H., Liu, T., Li, P., Xu, L., Dai, J., et al.: Image encryption by using gyrator transform and Arnold transform. J. Electron. Imaging 20(1), 013020 (2011). https://doi.org/10.1117/1.3557790
Liu, W., Liu, Z., Liu, S.: Asymmetric cryptosystem using random binary phase modulation based on mixture retrieval type of Yang-Gu algorithm. Opt. Lett. 38, 1651–1653 (2013). https://doi.org/10.1364/OL.38.001651
Lohmann, A.W.: Image rotation, Wigner rotation, and the fractional Fourier transform. JOSA A 10, 2181–2186 (1993). https://doi.org/10.1364/JOSAA.10.002181
Lü, J., Chen, G., Zhang, S.: Dynamical analysis of a new chaotic attractor. Int J Bifurcat Chaos 12, 1001–1015 (2002). https://doi.org/10.1142/S0218127402004851
Mehra, I., Nishchal, N.K.: Image fusion using wavelet transform and its application to asymmetric cryptosystem and hiding. Opt. Express 22, 5474–5482 (2014). https://doi.org/10.1364/OE.22.005474
Nishchal, N.K., Joseph, J., Singh, K.: Securing information using fractional Fourier transform in digital holography. Opt. Commun. 235, 253–259 (2004). https://doi.org/10.1016/j.optcom.2004.02.052
Nomura, T., Javidi, B.: Optical encryption using a joint transform correlator architecture. Opt. Eng. 39, 2031–2036 (2000). https://doi.org/10.1117/1.1304844
Peng, X., Zhang, P., Wei, H., Yu, B.: Known-plaintext attack on optical encryption based on double random phase keys. Opt. Lett. 31, 1044–1046 (2006). https://doi.org/10.1364/OL.31.001044
Poon, T.-C., Liu, J.-P. Introduction to Modern Digital Holography by Ting-Chung Poon. Camb Core 2014. https://doi.org/10.1017/cbo9781139061346
Qin, W.: Universal and special keys based on phase-truncated Fourier transform. Opt. Eng. 50(8), 080501 (2011). https://doi.org/10.1117/1.3607421
Qin, W., Peng, X.: Asymmetric cryptosystem based on phase-truncated Fourier transforms. Opt. Lett. 35, 118–120 (2010). https://doi.org/10.1364/OL.35.000118
Rajput, S.K., Nishchal, N.K.: Known-plaintext attack-based optical cryptosystem using phase-truncated Fresnel transform. Appl. Opt. 52, 871–878 (2013a). https://doi.org/10.1364/AO.52.000871
Rajput, S.K., Nishchal, N.K.: Known-plaintext attack on encryption domain independent optical asymmetric cryptosystem. Opt. Commun. 309, 231–235 (2013b). https://doi.org/10.1016/j.optcom.2013.06.036
Refregier, P., Javidi, B.: Optical image encryption based on input plane and Fourier plane random encoding. Opt. Lett. 20, 767–769 (1995). https://doi.org/10.1364/OL.20.000767
Rivest, R.L., Shamir, A., Adleman, L.: A method for obtaining digital signatures and public-key cryptosystems. Commun. ACM 21, 120–126 (1978). https://doi.org/10.1145/359340.359342
Sharma, N., Saini, I., Yadav, A., Singh, P.: Phase-image encryption based on 3D-Lorenz chaotic system and double random phase encoding. 3D Res (2017). https://doi.org/10.1007/s13319-017-0149-4
Singh, P., Yadav, A.K., Singh, K., Saini, I.: Optical image encryption in the fractional Hartley domain, using Arnold transform and singular value decomposition. AIP Conf. Proc. 1802, 020017 (2017a). https://doi.org/10.1063/1.4973267
Singh, P., Saini, I., Yadav, A.K.: Analysis of Lorenz-chaos and exclusive-OR based image encryption scheme. Int J Soc Comput Cyber Phys Syst 2, 59 (2017b). https://doi.org/10.1504/IJSCCPS.2017.10009739
Situ, G., Zhang, J.: Double random-phase encoding in the Fresnel domain. Opt. Lett. 29, 1584–1586 (2004). https://doi.org/10.1364/OL.29.001584
Smid, M.E., Branstad, D.K.: Data encryption standard: past and future. Proc. IEEE 76, 550–559 (1988). https://doi.org/10.1109/5.4441
Tajahuerce, E., Matoba, O., Verrall, S.C., Javidi, B.: Optoelectronic information encryption with phase-shifting interferometry. Appl. Opt. 39, 2313–2320 (2000). https://doi.org/10.1364/AO.39.002313
The Design of Rijndael—AES—the Advanced Encryption Standard|Joan Daemen|Springer. https://www.springer.com/in/book/9783540425809
Towghi, N., Javidi, B., Luo, Z.: Fully phase encrypted image processor. J. Opt. Soc. Am. A 16(8), 1915–1927 (1999). https://doi.org/10.1364/JOSAA.16.001915
Unnikrishnan, G., Joseph, J., Singh, K.: Optical encryption by double-random phase encoding in the fractional Fourier domain. Opt. Lett. 25, 887–889 (2000). https://doi.org/10.1364/OL.25.000887
Wang, Z., Sheikh, H.R.: Image quality assessment: from error visibility to structural similarity. IEEE Trans. Image Process. 13(4), 600–612 (2004). https://doi.org/10.1109/tip.2003.819861
Wang, X., Zhao, D.: Security enhancement of a phase-truncation based image encryption algorithm. Appl. Opt. 50, 6645–6651 (2011)
Wang, X., Zhao, D.: A special attack on the asymmetric cryptosystem based on phase-truncated Fourier transforms. Opt. Commun. 285, 1078–1081 (2012). https://doi.org/10.1016/j.optcom.2011.12.017
Wang, X., Zhao, D.: Simultaneous nonlinear encryption of grayscale and color images based on phase-truncated fractional Fourier transform and optical superposition principle. Appl. Opt. 52, 6170–6178 (2013a)
Wang, X., Zhao, D.: Amplitude-phase retrieval attack free cryptosystem based on direct attack to phase-truncated Fourier-transform-based encryption using a random amplitude mask. Opt. Lett. 38, 3684–3686 (2013b). https://doi.org/10.1364/OL.38.003684
Wang, X., Chen, Y., Dai, C., Zhao, D.: Discussion and a new attack of the optical asymmetric cryptosystem based on phase-truncated Fourier transform. Appl. Opt. 53, 208–213 (2014). https://doi.org/10.1364/AO.53.000208
Wang, Y., Quan, C., Tay, C.J.: Improved method of attack on an asymmetric cryptosystem based on phase-truncated Fourier transform. Appl. Opt. 54, 6874–6881 (2015). https://doi.org/10.1364/AO.54.006874
Wang, Y., Quan, C., Tay, C.J.: New method of attack and security enhancement on an asymmetric cryptosystem based on equal modulus decomposition. Appl. Opt. 55, 679–686 (2016)
Xu, H., Xu, W., Wang, S., Wu, S.: Asymmetric optical cryptosystem based on modulus decomposition in Fresnel domain. Opt. Commun. 402, 302–310 (2017). https://doi.org/10.1016/j.optcom.2017.05.035
Xu, H., Xu, W., Wang, S., Wu, S.: Phase-only asymmetric optical cryptosystem based on random modulus decomposition. J. Mod. Opt. 65, 1245–1252 (2018). https://doi.org/10.1080/09500340.2018.1431314
Zhou, N., Wang, Y., Gong, L.: Novel optical image encryption scheme based on fractional Mellin transform. Opt. Commun. 284, 3234–3242 (2011). https://doi.org/10.1016/j.optcom.2011.02.065
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Rakheja, P., Vig, R. & Singh, P. An asymmetric hybrid cryptosystem using equal modulus and random decomposition in hybrid transform domain. Opt Quant Electron 51, 54 (2019). https://doi.org/10.1007/s11082-019-1769-0
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11082-019-1769-0