Abstract
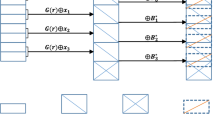
This paper addresses the issue of data governance in a cloud-based storage system. To achieve fine-grained access control over the outsourced data, we propose Self-Healing Attribute-based Privacy Aware Data Sharing in Cloud (SAPDS). The proposed system delegates the key distribution and management process to a cloud server without seeping out any confidential information. It facilitates data owner to restrain access of the user with whom data has been shared. User revocation is achieved by merely changing one attribute associated with the decryption policy, instead of modifying the entire access control policy. It enables authorized users to update their decryption keys followed by each user revocation, making it self-healing, without ever interacting with the data owner. Computation analysis of the proposed system shows that data owner can revoke n′ users with the complexity of O(n′). Besides this, legitimate users can update their decryption keys with the complexity of O(1).
Similar content being viewed by others
References
Armbrust M et al (2010) A view of cloud computing. Commun ACM 53:50–58
Kondo D, Javadi B, Malecot P, Cappello F, Anderson DP (2009) Cost-benefit analysis of cloud computing versus desktop grids. In: Proceedings of the 2009 IEEE international symposium on parallel&distributed processing. IEEE Computer Society, Washington, DC, pp 1–12
Assunção MD, Costanzo A, Buyya R (2010) A cost-benefit analysis of using cloud computing to extend the capacity of clusters. Clust Comput 13:335–347
Amazon Web Services LLC, Amazon Simple Storage Service (2009). http://aws.amazon.com/s3/
Amazon Web Services LLC, Amazon Elastic Compute Cloud (2009). http://aws.amazon.com/ec2/
Wood T, Gerber A, Ramakrishnan KK, Shenoy P, Van der Merwe J (2009) The case for enterprise-ready virtual private clouds. In: Proceedings of the 2009 conference on Hot topics in cloud computing, Berkeley, CA, USA, HotCloud’09, USENIX Association, p 4
Head MR, Sailer A, Shaikh H, Shea DG (2010) Towards self-assisted troubleshooting for the deployment of private clouds. In: Proceedings of the 2010 IEEE 3rd international conference on cloud computing, CLOUD ’10. IEEE Computer Society, Washington, DC, pp 156–163
Gartner Rating 2011. http://www.gartner.com/it/page.jsp?id=1454221
Naghshineh M et al (2009) Ibm research division cloud computing initiative. IBM J Res Dev 53:499–508
Pearson S (2009) Taking account of privacy when designing cloud computing services. In: Proceedings of the 2009 ICSE workshop on software engineering challenges of cloud computing, CLOUD ’09. IEEE Computer Society, Washington, DC, pp 44–52
Jaeger T, Schiffman J (2010) Outlook: Cloudy with a chance of security challenges and improvements. IEEE Secur Priv 8:77–80
Ristenpart T, Tromer E, Shacham H, Savage S (2009) Hey, you, get off of my cloud: exploring information leakage in third-party compute clouds. In: Proceedings of the 16th ACM conference on computer and communications security, CCS ’09. ACM, New York, pp 199–212
Michael B (2009) In clouds shall we trust? IEEE Secur Priv 7:3
Kaufman LM (2009) Data security in the world of cloud computing. IEEE Secur Priv 7:61–64
Pearson S, Charlesworth A (2009) Accountability as a way forward for privacy protection in the cloud. In: Proceedings of the 1st international conference on cloud computing, CloudCom ’09. Springer, Berlin, pp 131–144
U.S. Department of Health and Human Services, http://www.hhs.gov/ocr/privacy/ (2003) Protecting Personal Health Information in Research: Understanding the HIPAA Privacy Rule
Yekhanin S (2010) Private information retrieval. Commun ACM 53:68–73
Goh E-J, Shacham H, Modadugu N, Boneh D (2006) Sirius: Securing remote untrusted storage. In: Proceedings of the fifth workshop on the economics of information security (WEIS 2006)
Geron E, Wool A (2009) Crust: cryptographic remote untrusted storage without public keys. Int J Inf Secur 8:357–377
Fu K, Kamara S, Kohno T (2006) Key regression: Enabling efficient key distribution for secure distributed storage. In: Proc. network and distributed systems security symposium (NDSS)
Backes M, Oprea A (2005) Lazy revocation in cryptographic file systems. In: Proceedings of the third IEEE international security in storage workshop. IEEE Computer Society, Washington, DC, pp 1–11
Benaloh J, Chase M, Horvitz E, Lauter K (2009) Patient controlled encryption: ensuring privacy of electronic medical records. In: Proceedings of the 2009 ACM workshop on cloud computing security, CCSW ’09. ACM, New York, pp 103–114
Bethencourt J, Sahai A, Waters B (2007) Ciphertext-policy attribute-based encryption. In: Proceedings of the 2007 IEEE symposium on security and privacy, SP ’07. IEEE Computer Society, Washington, DC, pp 321–334
Ateniese G, Fu K, Green M, Hohenberger S (2006) Improved proxy re-encryption schemes with applications to secure distributed storage. ACM Trans Inf Syst Secur 9:1–30
Yu S, Wang C, Ren K, Lou W (2010) Achieving secure, scalable, and fine-grained data access control in cloud computing. In: Proceedings of the 29th conference on information communications, INFOCOM’10. IEEE Press, Piscataway, pp 534–542
Goyal V, Pandey O, Sahai A, Waters B (2006) Attribute-based encryption for fine-grained access control of encrypted data. In: Proceedings of the 13th ACM conference on computer and communications security, CCS ’06. ACM, New York, pp 89–98
Kallahalla M, Riedel E, Swaminathan R, Wang Q, Fu K (2003) Plutus: Scalable secure file sharing on untrusted storage. In: Proceedings of the 2nd USENIX conference on file and storage technologies. USENIX Association, Berkeley, pp 29–42
di Vimercati SDC, Foresti S, Jajodia S, Paraboschi S, Samarati P (2007) Over-encryption: management of access control evolution on outsourced data. In: Proceedings of the 33rd international conference on very large data bases, VLDB Endowment, VLDB ’07, pp. 123–134
Yu S, Wang C, Ren K, Lou W (2010) Attribute based data sharing with attribute revocation. In: Proceedings of the 5th ACM symposium on information, computer and communications security, ASIACCS ’10. ACM, New York, pp 261–270
Brickell E, Li J (2007) Enhanced privacy id: a direct anonymous attestation scheme with enhanced revocation capabilities. In: Proceedings of the 2007 ACM workshop on privacy in electronic society, WPES ’07. ACM, New York, pp 21–30
Jingmin He MW (2001) Cryptography and relational database management systems. In: Proceedings of the 2001 international symposium on database engineering & applications. IEEE Computer Society, Washington, DC, pp 273–284
Bethencourt J, Waters B, Sahai A Ciphertext-policy attribute-based encryption. http://acsc.cs.utexas.edu/cpabe/, accessed on Dec 10, 2010
Menezes AJ, Oorschot PCV, Vanstone SA, Rivest RL (1997) Handbook of applied cryptography
Google App Engine—Run your web applications on Google’s infrastructure. http://code.google.com/appengine/
Adams C, Farrell S (1999) Internet x.509 public key infrastructure certificate management protocols
Shamir A (1979) How to share a secret. Commun ACM 22:612–613
Interpolating Polynomial The Wolfram Demonstrations Project. http://demonstrations.wolfram.com/InterpolatingPolynomial/
Guo H, Viktor H, Paquet E (2011) Privacy disclosure and preservation in learning with multi-relational databases. J Comput Sci Eng 5(3):183–196
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Pervez, Z., Khattak, A.M., Lee, S. et al. SAPDS: self-healing attribute-based privacy aware data sharing in cloud. J Supercomput 62, 431–460 (2012). https://doi.org/10.1007/s11227-011-0727-9
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-011-0727-9