Abstract
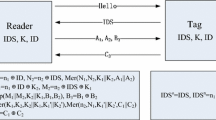
In this paper, we analyze the security of AZUMI protocol which is compliant with EPC-Class-1 Generation-2 standard and recently has been proposed by Peris et al. This protocol is an improvement to a protocol proposed by Chen and Deng which has been cryptanalysed by Peris et al. and Kapoor and Piramuthu. However, our security analysis clearly shows that the designers were not successful in their attempt to improve Chen and Deng protocol. More precisely, we present an efficient passive attack to disclose the tag and the reader secret parameters, due to PRNG and the length of the values. In addition, we present a simple tag impersonation attack against this protocol. The success probability of all attacks are almost “1” and the cost of given attacks are at most eavesdropping two sessions of protocol. However, the given secrets disclosure attack also requires \(O(2^{16})\) off-line evaluations of a \(PRNG\) function. To counteract such flaws, we improve the AZUMI protocol by applying some minor modifications so that it provides the claimed security properties.


Similar content being viewed by others
References
Bailey, D. V., & Juels, A. (2006). Shoehorning security into the EPC tag standard. In R. D. Prisco & M. Yung (Eds.), Security and cryptography for networks. 5th international conference, SCN 2006, Maiori, Italy, September 6-8, 2006, volume 4116 of, Lecture notes in computer science (pp. 303–320). Berlin: Springer, ISBN 3-540-38080-9.
Burmester, M. & de Medeiros, B. (2008) . The security of EPC gen2 compliant RFID protocols. In S. M. Bellovin, R. Gennaro, A. D. Keromytis, & M. Yung (Eds.), ACNS, volume 5037 of, Lecture Notes in Computer Science (pp. 490–506).
Burmester, M., de Medeiros, B., Munilla, J., & Peinado, A. (2009). Secure EPC gen2 compliant radio frequency identification. In P. M. Ruiz & J. J. Garcia-Luna-Aceves (Eds.), Ad-Hoc, mobile and wireless networks. 8th international conference, ADHOC-NOW2009, Murcia, Spain, September 22-25, volume 5793 of, Lecture notes in computer science (pp 227–240). Berlin: Springer, ISBN 978-3-642-04382-6.
Chen, C., He, D., Chan, S., Bu, J., Gao, Y., & Fan, R. (2011). Lightweight and provably secure user authentication with anonymity for the global mobility network. International Journal of Communication Systems, 24(3), 347–362.
Chen, C.-L., & Deng, Y.-Y. (2009). Conformation of EPC class 1 generation 2 standards RFID system with mutual authentication and privacy protection. Engineering Applications of Artificial Intelligence, 22(8), 1284–1291.
Chien, H.-Y., & Chen, C.-H. (2007). Mutual authentication protocol for RFID conforming to EPC class 1 generation 2 standards. Computer Standards & Interfaces, 29(2), 254–259.
Cho, K., Pack, S., Kwon, T. T., & Choi, Y. (2010). An extensible and ubiquitous rfid management framework over next-generation network. International Journal of Communication Systems, 23(9–10), 1093–1110.
Choi, E. Y., Lee, D. H., & Lim, J. I. (2009). Anti-cloning protocol suitable to EPC global class-1 generation-2 RFID systems. Computer Standards & Interfaces, 31(6), 1124–1130.
Class-1 generation 2 UHF air interface protocol standard version 1.2.0, Gen2 (2008). http://www.epcglobalinc.org/standards/
EPC Tag data standar dversion 1.4.2008. http://www.epcglobalinc.org/standards/. Yearly report on algorithms and keysizes. Technical report D.SPA.13Rev.1.0, ICT-2007-216676, In Gen2. ECRYPT, (2010).
Jin, G., Jeong, E. Y., Jung, H.-Y., & Lee, K. D. (2009). RFID authentication protocol conforming to EPC class-1 generation-2 standard. In H. R. Arabnia & K. Daimi (Eds.), International conference on security & management. SAM 2009, July 13–16, 2009, Las Vegas Nevada, USA (pp. 227–231). Nevada: CSREA Press, ISBN 1-60132-126-0.
Kapoor, G., & Piramuthu, S. (2011). Vulnerabilities in chen and dengs rfid mutual authentication and privacy protection protocol. Engineering Applications of Artificial Intelligence, 24(7), 1300–1302.
Kim, J. G., Shin, W. J., & Yoo, J. H. (2007). Performance analysis of EPC class-1 generation-2 RFID anti-collision protocol. In O. Gervasi & M. L. Gavrilova (Eds.), ICCSA (3), volume 4707 of Lecture notes in computer science (pp. 1017–1026). Berlin: Springer.
Li, J.-S., & Liu, K.-H. (2011). A hidden mutual authentication protocol for low-cost rfid tags. International Journal of Communication Systems, 24(9), 1196–1211.
Lo, N.-W., & Yeh, K.-H. (2007). An efficient mutual authentication scheme for EPCglobal class-1 generation-2 RFID system. In M. K. Denko, C.-S. Shih, K.-C. Li, S.-L. Tsao, Q.-A. Zeng, S.-H. Park, Y.-B. Ko, S.-H. Hung, & J. H. Park (Eds.), Emerging directions in embedded and ubiquitons computing. EUC 2007 Workshop: TRUST, WSOC, NCUS, UUWSN, USN, ESO, and SECUBIQ, Taipei, Taiwan, December 17-20, volume 4809 of, Lecture notes in computer science (pp. 43–56). Berlin: Springer.
Meiller, Y., Bureau, S., Zhou, W., & Piramuthu, S. (2011). Adaptive knowledge-based system for health care applications with rfid-generated information. Decision Support Systems, 51(1), 198–207.
Peris-Lopez, P., Hernandez-Castro, J. C., Estevez-Tapiador, J. M., & Ribagorda, A. (2008). RFID specification revisited. In The internet of things: From RFID to the next-generation pervasive networked systems (pp. 311–346). Auerbach publications, Taylor & Francis Group.
Peris-Lopez, P., Hernandez-Castro, J. C., Estévez-Tapiador, J. M., & Ribagorda, A. (2009). Cryptanalysis of a novel authentication protocol conforming to EPC-C1G2 standard. Computer Standards & Interfaces, 31(2), 372–380.
Peris-Lopez, P., Hernandez-Castro, J. C., Tapiador, J. E., & van der Lubbe, J. C. A. (2011). Cryptanalysis of an EPC class-1 generation-2 standard compliant authentication protocol. Engineering Applications of Artificial Intelligence, 24(6), 1061–1069.
Peris-Lopez, P., Li, T., & Hernandez-Castro, J. C. (2010). Lightweight props on the weak security of EPC class-1 generation-2 standard. IEICE Transactions, 93–D(3), 518–527.
Peris-Lopez, P., Li, T., Hernandez-Castro, J. C., & Tapiador, J. E. (2009). Practical attacks on a mutual authentication scheme under the EPC class-1 generation-2 standard. Computer Communications, 32(7–10), 1185–1193.
Peris-Lopez, P., Orfila, A., Mitrokotsa, A., & van der Lubbe, J. C. A. (2011). A comprehensive rfid solution to enhance inpatient medication safety. International Journal of Medical Informatics, 80(1), 13–24.
Piramuthu, S. (2007). Protocols for rfid tag/reader authentication. Decision Support Systems, 43(3), 897–914.
Piramuthu, S. (2011). Rfid mutual authentication protocols. Decision Support Systems, 50(2), 387–393.
Safkhani, M., Bagheri, N., Sanadhya, S. K. & Naderi, M. (2011). Cryptanalysis of improved yeh et al’.s authentication protocol: An epc class-1 generation-2 standard compliant protocol. IACR Cryptology ePrint Archive, 426 2011.
Sun, Q., Zhang, H., & Mo, L. (2011). Dual-reader wireless protocols for dense active rfid identification. International Journal of Communication Systems, 24(11), 1431–1444.
Vaidya, B., Rodrigues, J. J. P. C., & Park, J. H. (2010). User authentication schemes with pseudonymity for ubiquitous sensor network in ngn. International Journal of Communication Systems, 23(9–10), 1201–1222.
Wickboldt, A.-K., & Piramuthu, S. (2012). Patient safety through rfid: Vulnerabilities in recently proposed grouping protocols. Journal of Medical Systems, 36(2), 431–435.
Yeh, K.-H., & Lo, N.-W. (2009). Improvement of an EPC gen2 compliant RFID authentication protocol. In IAS (pp. 532–535). IEEE Computer Society.
Yeh, K.-H., Lo, N.-W., & Li, Y. (2011). Cryptanalysis of hsiang-shih’s authentication scheme for multi-server architecture. International Journal of Communication Systems, 24(7), 829–836.
Yeh, T.-C., Wang, Y.-J., Kuo, T.-C., & Wang, S.-S. (2010). Securing RFID systems conforming to EPC class 1 generation 2 standard. Expert Systems with Applications, 37(12), 7678–7683.
Yoon, E.-J. (2012). Improvement of the securing RFID systems conforming to EPC class 1 generation 2 standard. Expert Systems with Applications, 32(1), 1589–1594.
Zhou, W., & Piramuthu, S. (2011). Combining fuzzy evidence from hb protocol variant for rfid authentication in supply chains. In FSKD (pp. 816–819). IEEE.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Safkhani, M., Bagheri, N. & Naderi, M. Strengthening the Security of EPC C-1 G-2 RFID Standard. Wireless Pers Commun 72, 1295–1308 (2013). https://doi.org/10.1007/s11277-013-1078-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-013-1078-z