Abstract
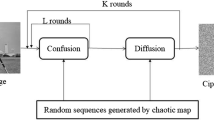
Chaotic maps are extensively utilized in the field of image encryption to generate secret keys. However, these maps suffer from hyper-parameters tuning issues. These parameters are generally selected on hit and trial basis. However, inappropriate selection of these parameters may reduce the performance of chaotic maps. Also, these hyper-parameters are not sensitive to input images. Therefore, in this paper, to handle these issues, a non-dominated sorting genetic algorithm-III (NSGA) based 4-D chaotic map is designed. Additionally, to improve the computational speed of the proposed approach, we have designed a novel master-slave model for image encryption. Initially, computationally expensive operations such as mutation and crossover of NSGA-III are identified. Thereafter, NSGA-III parameters are split among two jobs, i.e., master and slave jobs. For communication between master and slave nodes, the message passing interface is used. Extensive experimental results reveal that the proposed image encryption technique outperforms the existing techniques in terms of various performance measures.
















Similar content being viewed by others
References
Afarin R, Mozaffari S (2013) Image encryption using genetic algorithm. In: 2013 8th Iranian conference on machine vision and image processing (MVIP), IEEE, pp 441–445
Belazi A, El-Latif AAA, Belghith S (2016) A novel image encryption scheme based on substitution-permutation network and chaos. Signal Process 128:155–170
Chatterjee A, Dhanotia J, Bhatia V, Rana S, Prakash S (2017) Optical image encryption using fringe projection profilometry, Fourier Fringe analysis, and RSA algorithm. In: 2017 14th IEEE India council international conference (INDICON), IEEE, pp 1–5
Chen G, Mao Y, Chui CK (2004) A symmetric image encryption scheme based on 3d chaotic cat maps. Chaos Solitons Fractals 21(3):749–761
Chuman T, Sirichotedumrong W, Kiya H (2019) Encryption-then-compression systems using grayscale-based image encryption for JPEG images. IEEE Trans Inf Forensics Secur 14(6):1515–1525
Ciro GC, Dugardin F, Yalaoui F, Kelly R (2016) A nsga-ii and nsga-iii comparison for solving an open shop scheduling problem with resource constraints. IFAC-PapersOnLine 49(12):1272–1277
Das R, Manna S, Dutta S (2017) Cumulative image encryption approach based on user defined operation, character repositioning, text key and image key encryption technique and secret sharing scheme. In: 2017 IEEE international conference on power, control, signals and instrumentation engineering (ICPCSI), IEEE, pp 748–753
Du S, Qiu D, Mateus P, Gruska J (2019) Enhanced double random phase encryption of quantum images. Results Phys 13:102161
El Assad S, Farajallah M (2016) A new chaos-based image encryption system. Signal Process Image Commun 41:144–157
Gao H, Zhang Y, Liang S, Li D (2006) A new chaotic algorithm for image encryption. Chaos Solitons Fractals 29(2):393–399
Gao T, Chen Z (2008) A new image encryption algorithm based on hyper-chaos. Phys Lett A 372(4):394–400
Hua Z, Zhou Y (2016) Image encryption using 2d logistic-adjusted-sine map. Inf Sci 339:237–253
Kaur M, Kumar V (2018a) Adaptive differential evolution-based lorenz chaotic system for image encryption. Arab J Sci Eng 43(12):8127–8144
Kaur M, Kumar V (2018b) Beta chaotic map based image encryption using genetic algorithm. Int J Bifurc Chaos 28(11):1850132
Kaur M, Kumar V (2018c) Colour image encryption technique using differential evolution in non-subsampled contourlet transform domain. IET Image Process 12(7):1273–1283
Kaur M, Kumar V (2018d) A comprehensive review on image encryption techniques. Arch Comput Methods Eng. https://doi.org/10.1007/s11831-018-9298-8
Kaur M, Kumar V (2018e) Fourier-mellin moment-based intertwining map for image encryption. Mod Phys Lett B 32(09):1850115
Kaur M, Kumar V (2018f) Parallel non-dominated sorting genetic algorithm-II-based image encryption technique. Imaging Sci J 66(8):453–462
Kaur M, Kumar V, Li L (2018) Color image encryption approach based on memetic differential evolution. Neural Comput Appl. https://doi.org/10.1007/s00521-018-3642-7
Ke L, Yi Z, Ren Y (2015) Improved broadcast encryption schemes with enhanced security. J Ambient Intell Humaniz Comput 6(1):121–129
Lang J (2012) The reality-preserving multiple-parameter fractional fourier transform and its application to image encryption. In: 2012 5th international congress on image and signal processing, IEEE, pp 1153–1157
Lei Z, Li L, Xianwei G (2011) Design and realization of image encryption system based on sms4 commercial cipher algorithm. In: 2011 4th international congress on image and signal processing, IEEE, vol 2, pp 741–744
Li C (2016) Cracking a hierarchical chaotic image encryption algorithm based on permutation. Signal Process 118:203–210
Li X, Zhang G, Zhang X (2015) Image encryption algorithm with compound chaotic maps. J Ambient Intell Humaniz Comput 6(5):563–570
Lin J, Luo Y, Liu J, Bi J, Qiu S, Cen M, Liao Z (2018) An image compression-encryption algorithm based on cellular neural network and compressive sensing. In: 2018 IEEE 3rd international conference on image, vision and computing (ICIVC), IEEE, pp 673–677
Liu W, Sun K, Zhu C (2016) A fast image encryption algorithm based on chaotic map. Opt Lasers Eng 84:26–36
Mondal B, Mandal T (2017) A light weight secure image encryption scheme based on chaos and DNA computing. J King Saud Univ Comput Inf Sci 29(4):499–504
Pak C, Huang L (2017) A new color image encryption using combination of the 1d chaotic map. Signal Process 138:129–137
Pareek NK, Patidar V, Sud KK (2006) Image encryption using chaotic logistic map. Image Vis Comput 24(9):926–934
Ramaraju P, Raju GN, Krishna PR (2016) Image encryption after hiding (IEAH) technique for color images. In: 2016 international conference on signal processing, communication, power and embedded system (SCOPES), IEEE, pp 1202–1207
Saini JK, Verma HK (2013) A hybrid approach for image security by combining encryption and steganography. In: 2013 IEEE second international conference on image information processing (ICIIP-2013), IEEE, pp 607–611
Sambas A, Mamat M, Viadyanathan S, Mohamed MA, Sanjaya WM (2018) A new 4-d chaotic system with hidden attractor and its circuit implementation. Int J Eng Technol 7(3):1245–1250
Shaheen AM, Sheltami TR, Al-Kharoubi TM, Shakshuki E (2018) Digital image encryption techniques for wireless sensor networks using image transformation methods: DCT and DWT. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-018-0850-z
Shankar K, Elhoseny M, Kumar RS, Lakshmanaprabu S, Yuan X (2018) Secret image sharing scheme with encrypted shadow images using optimal homomorphic encryption technique. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-018-1161-0
Shao Z, Wu J, Coatrieux JL, Coatrieux G, Shu H (2013) Quaternion gyrator transform and its application to color image encryption. In: 2013 IEEE international conference on image processing, IEEE, pp 4579–4582
Singh PK, Singh RS, Rai KN (2015) An image encryption algorithm based on XOR operation with approximation component in wavelet transform. In: 2015 Fifth national conference on computer vision, pattern recognition, image processing and graphics (NCVPRIPG), IEEE, pp 1–4
Sneha P, Sankar S, Kumar AS (2019) A chaotic colour image encryption scheme combining Walsh–Hadamard transform and Arnold–Tent maps. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-019-01385-0
Wang XY, Zhang YQ, Bao XM (2015) A novel chaotic image encryption scheme using dna sequence operations. Opt Lasers Eng 73:53–61
Wen W, Zhang Y, Fang Y, Fang Z (2016) A novel selective image encryption method based on saliency detection. In: 2016 visual communications and image processing (VCIP), IEEE, pp 1–4
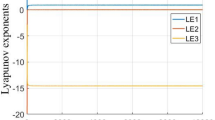
Wolf A, Swift JB, Swinney HL, Vastano JA (1985) Determining Lyapunov exponents from a time series. Phys D Nonlinear Phenom 16(3):285–317
Xu L, Li Z, Li J, Hua W (2016) A novel bit-level image encryption algorithm based on chaotic maps. Opt Lasers Eng 78:17–25
Xu Y, Wu S, Wang M, Zou Y (2018) Design and implementation of distributed RSA algorithm based on Hadoop. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-018-1021-y
Ye G (2010) Image scrambling encryption algorithm of pixel bit based on chaos map. Pattern Recognit Lett 31(5):347–354
Yi JH, Deb S, Dong J, Alavi AH, Wang GG (2018) An improved NSGA-III algorithm with adaptive mutation operator for big data optimization problems. Future Gener Comput Syst 88:571–585
Zhou Y, Agaian S (2011) Image encryption using the image steganography concept and plip model. In: Proceedings 2011 international conference on system science and engineering, IEEE, pp 699–703
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Gupta, A., Singh, D. & Kaur, M. An efficient image encryption using non-dominated sorting genetic algorithm-III based 4-D chaotic maps. J Ambient Intell Human Comput 11, 1309–1324 (2020). https://doi.org/10.1007/s12652-019-01493-x
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12652-019-01493-x