Abstract
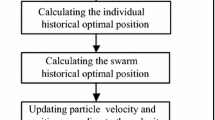
The leaking of sensitive data on Android mobile device poses a serious threat to users, and the unscrupulous attack violates the privacy of users. Therefore, an effective Android malware detection system is necessary. However, detecting the attack is challenging due to the similarity of the permissions in malware with those seen in benign applications. This paper aims to evaluate the effectiveness of the machine learning approach for detecting Android malware. In this paper, we applied the bio-inspired algorithm as a feature optimization approach for selecting reliable permission features that able to identify malware attacks. A static analysis technique with machine learning classifier is developed from the permission features noted in the Android mobile device for detecting the malware applications. This technique shows that the use of Android permissions is a potential feature for malware detection. The study compares the bio-inspired algorithm [particle swarm optimization (PSO)] and the evolutionary computation with information gain to find the best features optimization in selecting features. The features were optimized from 378 to 11 by using bio-inspired algorithm: particle swarm optimization (PSO). The evaluation utilizes 5000 Drebin malware samples and 3500 benign samples. In recognizing the Android malware, it appears that AdaBoost is able to achieve good detection accuracy with a true positive rate value of 95.6%, using Android permissions. The results show that particle swarm optimization (PSO) is the best feature optimization approach for selecting features.
Similar content being viewed by others
References
Nokia: Nokia Malware Report Shows Surge in Mobile Device Infections in 2016. http://company.nokia.com/en/news/press-releases/2016/09/01/nokia-malware-report-shows-surge-in-mobile-device-infections-in-2016
Symantec Corporation: Internet Security Threat Report (2016)
Fionna Agomuoh: “Godless” Android Malware Could Infect 90 Percent Of Google-Based Smartphones: How to Protect Your Device. http://www.idigitaltimes.com/godless-android-malware-could-infect-90-percent-google-based-smartphones-how-protect-542161
Conner Forrest: HummingBad Malware Infects 10 Million Android Devices, Millions More at Risk. http://www.techrepublic.com/article/hummingbad-malware-infects-10-million-android-devices-millions-more-at-risk/
Tam, K.; Feizollah, A.L.I.; Anuar, N.O.R.B.; Salleh, R.; Cavallaro, L.: The evolution of android malware and android analysis techniques. ACM Comput. Surv. 49, 1–41 (2017)
Martin Zhang: Android Ransomware Variant Uses Clickjacking to Become Device Administrator. https://www.symantec.com/connect/blogs/android-ransomware-variant-uses-clickjacking-become-device-administrator
Razak, M.F.A.; Anuar, N.B.; Salleh, R.; Firdaus, A.: The rise of “malware”: bibliometric analysis of malware study. J. Netw. Comput. Appl. 75, 58–76 (2016)
Tegawend, K.A.; Bissyand, F.; Quentin, J.; Radu, K.; Le, Traon Y.: Empirical assessment of machine learning-based malware detectors for Android measuring the gap between in-the-lab and in-the-wild validation scenarios. Empir. Softw. Eng. 21, 183–211 (2016)
Narudin, F.A.; Feizollah, A.; Anuar, N.B.; Gani, A.: Evaluation of machine learning classifiers for mobile malware detection. Soft. Comput. 20, 343–357 (2016)
Gheorghe, L.; Marin, B.; Gibson, G.; Mogosanu, L.; Deaconescu, R.; Voiculescu, V.-G.; Carabas, M.: Smart malware detection on Android. Secur. Commun. Netw. 8, 4254–4272 (2015)
Afifi, F.; Anuar, N.B.; Shamshirband, S.; Choo, K.-K.R.: DyHAP: dynamic hybrid ANFIS-PSO approach for predicting mobile malware. PLoS ONE 11, e0162627 (2016)
Aafer, Y.; Du, W.; Yin, H.: DroidAPIMiner: mining API-level features for robust malware detection in android. Secur. Priv. Commun. Netw. 127, 86–103 (2013)
Talha, K.A.; Alper, D.I.; Aydin, C.: APK Auditor: permission-based Android malware detection system. Digital Investig. 13, 1–14 (2015)
Suarez-tangil, G.; Tapiador, J.E.; Peris-lopez, P.; Blasco, J.: DENDROID: a text mining approach to analyzing and classifying code structures in Android malware families. Expert Syst. Appl. 41, 1104–1117 (2014)
Firdaus, A.; Anuar, N.B.; Razak, M.F.A.; Sangaiah, A.K.: Bio-inspired computational paradigm for feature investigation and malware detection: interactive analytics. Multimed. Tools Appl. (2017). https://doi.org/10.1007/s11042-017-4586-0
Yuan, Z.; Lu, Y.; Xue, Y.: DroidDetector: Android malware characterization and detection using deep learning. Tsinghua Sci. Technol. 21, 114–123 (2016)
Suleiman, Y.; Yerima, S.S.; Muttik, I.: High accuracy android malware detection using ensemble learning. IET Inf. Secur. 9, 313–320 (2015)
SAS Enterprise: Machine Learning. http://www.sas.com/it_it/insights/analytics/machine-learning.html
Allix, K.; Bissyandé, T.F.; Jérome, Q.; Klein, J.; State, R.; Le Traon, Y.: Empirical assessment of machine learning-based malware detectors for Android: measuring the gap between in-the-lab and in-the-wild validation scenarios. Empir. Softw. Eng. 21, 183–211 (2016)
Bhuyan, M.H.; Bhattacharyya, D.K.; Kalita, J.K.: Network anomaly detection: methods, systems and tools. IEEE Commun. Surv. Tutor. 16, 303–336 (2014)
Sheen, S.; Anitha, R.; Natarajan, V.: Android based malware detection using a multifeature collaborative decision fusion approach. Neurocomputing 151, 905–912 (2015)
Zhao, M.; Zhang, T.; Ge, F.; Yuan, Z.: RobotDroid: a lightweight malware detection framework on smartphones. J. Netw. 7, 715–722 (2012)
Adewole, K.S.; Anuar, N.B.; Kamsin, A.; Varathan, K.D.; Razak, S.A.: Malicious accounts: dark of the social networks. J. Netw. Comput. Appl. 79, 41–67 (2017)
Egele, M.; Scholte, T.; Kirda, E.; Kruegel, C.: A survey on automated dynamic malware analysis techniques and tools. ACM Comput. Surv. (CSUR) 44(2), 1–49 (2012)
Veerwal, D.; Menaria, P.: Ensemble of soft computing techniques for malware detection. Int. J. Emerg. Technol. Comput. Appl. Sci. (IJETCAS) 6, 159–167 (2013)
Firdaus, A.; Anuar, N.B.; Karim, A.; Razak, M.F.A.; Discovering optimal features using static analysis and genetic search based method for android malware detection. Front. Inf. Technol. Electron. Eng. (2017). https://doi.org/10.1631/FITEE.1601491
Wang, Y., Zheng, J., Sun, C., Mukkamala, S.: Quantitative security risk assessment of Android permissions and applications. In: Data and Applications Security and Privacy, vol. XXVII, pp. 226–241 (2013)
Zhou, Y.; Jiang, X.: Dissecting Android malware: characterization and evolution. In: 2012 IEEE Symposium on Security and Privacy, pp. 95–109 (2012)
Enck, W.; Gilbert, P.; Chun, B.-G.; Cox, L.P.; Jung, J.; McDaniel, P.; Sheth, A.N.: TaintDroid: an information-flow tracking system for realtime privacy monitoring on smartphones. ACM Trans. Comput. Syst. (TOCS) 32, 1–29 (2014)
Tchakounte, F.: Permission-based malware detection mechanisms on Android: analysis and perspectives. J. Comput. Sci. Softw. Appl. 1, 63–77 (2014)
Institute, I.: Importance of Security in Mobile Platforms. http://resources.infosecinstitute.com/importance-of-security-in-mobile-platforms/
Aung, Z.; Zaw, W.: Permission-based android malware detection. Int. J. Sci. Technol. Res. 2, 228–234 (2013)
Developer, A.: Android Permission. https://developer.android.com/guide/topics/security/permissions.html
Developer, A.: Android Permission. http://developer.android.com/guide/topics/manifest/permission-element.html
Feizollah, A.; Anuar, N.B.; Salleh, R.; Suarez-Tangil, G.; Furnell, S.: AndroDialysis: analysis of android intent effectiveness in malware detection. Comput. Secur. 65, 121–134 (2017)
Fang, Z.; Han, W.; Li, Y.: Permission based Android security: issues and countermeasures. Comput. Secur. 43, 205–218 (2014)
Liao, H.-J.; Richard Lin, C.-H.; Lin, Y.-C.; Tung, K.-Y.: Intrusion detection system: a comprehensive review. J. Netw. Comput. Appl. 36, 16–24 (2012)
Xue, B.; Zhang, M.J.; Browne, W.N.: Particle swarm optimization for feature selection in classification: a multi-objective approach. IEEE Trans. Cybern. 43, 1656–1671 (2013)
Sujithra, M.; Padmavathi, G.: Enhanced permission based malware detection in mobile devices using optimized random forest classifier with PSO-GA. Res. J. Appl. Sci. Eng. Technol. 12, 732–741 (2016)
Liu, Y.; Wang, G.; Chen, H.; Dong, H.: An improved particle swarm optimization for feature selection. J. Bionic Eng. 8, 191–200 (2011)
Adebayo, O.S.; AbdulAziz, N.: Android malware classification using static code analysis and Apriori algorithm improved with particle swarm optimization. In: 2014 Fourth World Congress on Information and Communication Technologies (WICT), pp. 123–128 (2014)
Ahmad, I.: Feature selection using particle swarm optimization. Int. J. Sens. Netw. 2015, 1–8 (2015)
Kumar, V.; Minz, S.: Feature selection: a literature review. Smart Comput. Rev. 4, 211–229 (2014)
Arp, D.; Spreitzenbarth, M.; Malte, H.; Gascon, H.; Rieck, K.: Drebin: Effective and explainable detection of android malware in your pocket. In: Symposium on Network and Distributed System Security (NDSS), pp. 1–15 (2014)
McWilliams, G.; Sezer, S.; Yerima, S.Y.: Analysis of Bayesian classification-based approaches for Android malware detection. IET Inf. Secur. 8, 25–36 (2014)
Allix, K.; Bissyandé, T.F.; Klein, J.; Le Traon, Y.: AndroZoo: collecting millions of Android apps for the research community. In: 13th International Workshop on Mining Software Repositories-MSR ’16, pp. 468–471 (2016)
Elish, K.O.; Shu, X.; Yao, D.D.; Ryder, B.G.; Jiang, X.: Profiling user-trigger dependence for Android malware detection. Comput. Secur. 49, 255–273 (2015)
Somarriba, O.; Zurutuza, U.; Uribeetxeberria, R.; Delosières, L.; Nadjm-tehrani, S.: Detection and visualization of android malware behavior. J. Electr. Comput. Eng. 2016, 1–17 (2016)
Zhang, Y.; Lee, W.; Huang, Y.-A.: Intrusion detection techniques for mobile wireless networks. Wirel. Netw. 9, 545–556 (2003)
Shabtai, A.; Kanonov, U.; Elovici, Y.; Glezer, C.; Weiss, Y.: “Andromaly”: a behavioral malware detection framework for android devices. J. Intell. Inf. Syst. 38, 161–190 (2012)
Gaviria, J.; Puerta, D.; Sanz, B.; Grueiro, I.S.; Bringas, P.G.: The evolution of permission as feature for AndroidMalware detection. In: International Joint Conference, Advances in Intelligent Systems and Computing, p. 761 (2013)
Wu, D.-J.; Mao, C.-H.; Wei, T.-E.; Lee, H.-M.; Wu, K.-P.: DroidMat: Android malware detection through manifest and API calls tracing. In: 2012 Seventh Asia Joint Conference on Information Security, pp. 62–69 (2012)
Fawcett, T.: An introduction to ROC analysis. Pattern Recogn. Lett. 27, 861–874 (2006)
Author information
Authors and Affiliations
Corresponding authors
Rights and permissions
About this article
Cite this article
Razak, M.F.A., Anuar, N.B., Othman, F. et al. Bio-inspired for Features Optimization and Malware Detection. Arab J Sci Eng 43, 6963–6979 (2018). https://doi.org/10.1007/s13369-017-2951-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-017-2951-y