Abstract
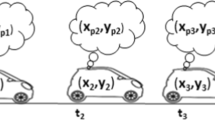
Location-based services (LBS), which provide personalized and timely information, entail privacy concerns such as unwanted leaks of current user locations to potential stalkers. In this regard, existing works have proposed dummy generation techniques by creating a cloaking region (CR) such that the user’s location is at a fixed distance from the centre of CR. Hence, if the adversary somehow knows the location of the centre of CR, the user’s location would be vulnerable to attacks. Moreover, in case of the existing approaches, infeasible regions are assumed to have no relationship with time. However, this assumption is typically not valid in real-world scenarios. For example, a supermarket can be considered to be an infeasible region from 9 pm to 9 am since it would be closed at that time. Thus, if a dummy is placed at this location at that particular time, the attacker would know that it is a dummy, thereby reducing the user’s location privacy. In this regard, our key contributions are three-fold. First, we propose an improved dummy generation approach, which we designate as Annulus-based Gaussian Dummy Generation (AGDG), for facilitating improved location privacy for mobile users. Second, we introduce the notion of time-dependent infeasible regions to further improve the dummy generation approach by considering infeasible regions that change with time. Third, we conducted experiments to demonstrate that the AGDG effectively provides improved location privacy, including for regions with time-dependent infeasible regions w.r.t. existing approaches.



















Similar content being viewed by others
References
Gruteser M, Hoh B (2005) On the anonymity of periodic location samples. In: Proceedings of the 2nd international conference on security in pervasive computing, pp 179–192
Hoh B, Gruteser M (2005) Protecting location privacy through path confusion. In: Proceedings of the 1st international conference on security and privacy for emerging areas in communications networks, pp 194–205
Bradbury M, Taylor P, Atmaca UI, Maple C, Griffiths N (2020) Privacy challenges with protecting live vehicular location context. IEEE Access 8:207465–207484
Burmeister F, Drews P, Schirmer I (2021) Modeling the C(o)urse of privacy-critical location-based services–exposing dark side archetypes of location tracking. In: Proceedings of the 54th hawaii international conference on system sciences, pp 6651– 6660
Matsuo Y, Okazaki N, Izumi K, Nakamura Y, Nishimura T, Hasida K, Nakashima H (2007) Inferring long-term user properties based on users’ location history. In: Proceedings of the 20th international joint conferences on artificial intelligence, pp 2159–2165
Voelcker J (2006) Stalked by satellite: An alarming rise in GPS-enabled harassment. IEEE Spectr 43(7):15–16
Cheng R, Zhang Y, Bertino E, Prabhakar S (2006) Preserving user location privacy in mobile data management infrastructures. In: Proceedings of the international workshop on privacy enhancing technologies, pp 393–412
Chow C-Y, Mokbel MF, Liu X (2011) Spatial cloaking for anonymous location-based services in mobile peer-to-peer environments. GeoInformatica 15(2):351–380
Liu S, Wang JH, Wang J, Zhang Q (2020) Achieving user-defined location privacy preservation using a P2P system. IEEE Access 8:45895–45912
Gedik B, Liu L (2005) Location privacy in mobile systems: a personalized anonymization model. In: Proceedings of the 25th international conference on distributed computing systems, pp 620–629
Ghinita G, Kalnis P, Skiadopoulos S (2007) Mobihide: A mobilea peer-to-peer system for anonymous location-based queries. In: Proceedings of the 10th international symposium on spatial and temporal databases, pp 221–238
Gruteser M, Grunwald D (2003) Anonymous usage of location-based services through spatial and temporal cloaking. In: Proceedings of the 1st international conference on mobile systems, applications and services, pp 31–42
Niu B, Li Q, Zhu X, Cao G, Li H (2014) Achieving k-anonymity in privacy-aware location-based services. In: Proceedings of the international conference on computer communications, pp 754–762
Qiu Y, Liu Y, Li X, Chen J (2020) A novel location privacy-preserving approach based on blockchain. Sensors 20(12):3519–3537
Lee B, Oh J, Yu H, Kim J (2011) Protecting location privacy using location semantics. In: Proceedings of the 17th international conference on knowledge discovery and data mining, pp 1289–1297
Ardagna CA, Cremonini M, di Vimercati SDC, Samarati P (2009) An obfuscation-based approach for protecting location privacy. Dependable and Secure Computing 8(1):13–27
Ardagna CA, Cremonini M, Damiani E, Di Vimercati SDC, Samarati P (2007) Location privacy protection through obfuscation-based techniques. In: Proceedings of the 21st annual IFIP working conference on data and applications security, pp 47–60
Bordenabe NE, Chatzikokolakis K, Palamidessi C (2014) Optimal geo-indistinguishable mechanisms for location privacy. In: Proceedings of the 16th international conference on computer and communications security, pp 251–262
Duckham M, Kulik L (2005) A formal model of obfuscation and negotiation for location privacy. In: Proceedings of the 3rd international conference on pervasive computing, pp 152–170
Khoshgozaran A, Shahabi C (2007) Blind evaluation of nearest neighbor queries using space transformation to preserve location privacy. In: Proceedings of the 10th international symposium on spatial and temporal databases, pp 239–257
Ullah I, Shah MA, Khan A, Jeon G (2021) Privacy-preserving multilevel obfuscation scheme for vehicular network. Transactions on Emerging Telecommunications Technologies 32(2):4204–4230
Shahid AR, Pissinou N, Iyengar S, Makki K (2020) Delay-aware privacy-preserving location-based services under spatiotemporal constraints. Int J Commun Syst 34(1):1–10
Xiong P, Li G, Ren W, Zhu T (2021) LOPO: A location privacy preserving path optimization scheme for spatial crowdsourcing. Journal of Ambient Intelligence and Humanized Computing 1–16
Ji Y, Gui R, Gui X, Liao D, Lin X (2020) Location privacy protection in online query based-on privacy region replacement. In: Proceedings of the 10th annual computing and communication workshop and conference, pp 742–747
Cai T-Y, Song D-H, Youn J-H, Lee W-G, Kim Y-K, Park K-J (2016) Efficient dummy generation for protecting location privacy. The Journal of Korea Institute of Information Electronics, and Communication Technology 9(6):526–533
Hara T, Suzuki A, Iwata M, Arase Y, Xie X (2016) Dummy-based user location anonymization under real-world constraints. IEEE Access 4:673–687
Song D, Song M, Shakhov V, Park K (2021) Efficient dummy generation for considering obstacles and protecting user location. Concurrency and Computation: Practice and Experience 33(2):5146–5156
Zhao H, Wan J, Chen Z (2016) A novel dummy-based kNN query anonymization method in mobile services. International Journal of Smart Home 10(6):137–154
Siddiqie S, Mondal A, Krishna Reddy P (2021) An improved dummy generation approach for enhancing user location privacy. In: Proceedings of the 26th international conference on database systems for advanced applications, pp 487–495
Zhou B, Pei J (2011) The k-anonymity and l-diversity approaches for privacy preservation in social networks against neighborhood attacks. Knowl Inf Syst 28(1):47–77
Krumm J (2007) Inference attacks on location tracks. In: Proceedings of the 5th international conference on pervasive computing, pp 127–143
Niu B, Zhang Z, Li X, Li H (2014) Privacy-area aware dummy generation algorithms for location-based services. In: Proceedings of the 1st international conference on communications, pp 957–962
Boccaletti S, Bianconi G, Criado R, Del Genio CI, Gómez-Gardenes J, Romance M, Sendina-Nadal I, Wang Z, Zanin M (2014) The structure and dynamics of multilayer networks. Phys Rep 544(1):1–122
Serjantov A, Danezis G (2002) Towards an information theoretic metric for anonymity. In: Proceedings of the 2nd international workshop on privacy enhancing technologies, pp 41–53
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Anirban Mondal and P Krishna Reddy are contributed equally to this work.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Siddiqie, S., Mondal, A. & Reddy, P.K. An improved dummy generation approach for infeasible regions. Appl Intell 53, 18700–18714 (2023). https://doi.org/10.1007/s10489-022-04379-2
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10489-022-04379-2